A New Global Phishing Threat: What You Need to Know About the Latest Microsoft 365 Scam
TechSquad Daniel | Posted on |

Cybersecurity researchers have recently uncovered a fast‑growing phishing campaign targeting Microsoft 365 users across the world. First detected on February 19, 2026, the operation has quickly expanded to more than 340 organizations in countries like the U.S., Canada, Australia, New Zealand, and Germany. From construction companies and hospitals to law firms, financial institutions, manufacturers, and even non‑profits no industry has been spared.
While phishing attacks are nothing new, this one stands out for its scale, sophistication, and the sneaky tactics attackers are using to trick everyday users.
How Attackers Are Tricking People
This campaign uses a variety of believable messages crafted to get your attention and prompt quick action. These include things like:
- Fake construction project bids
- Bogus DocuSign requests
- Phony voicemail alerts
- Misleading Microsoft Forms messages
No matter which lure the attackers use, the end goal is always the same: convincing you to interact with a fraudulent login process that secretly hands over access to your account.
Even more concerning is how the attackers hide their tracks. They use trusted cloud services like Cloudflare and Vercel, plus carefully crafted redirect chains, to sneak past email security filters and make the scam look legitimate.
What Makes Device Code Phishing So Dangerous?
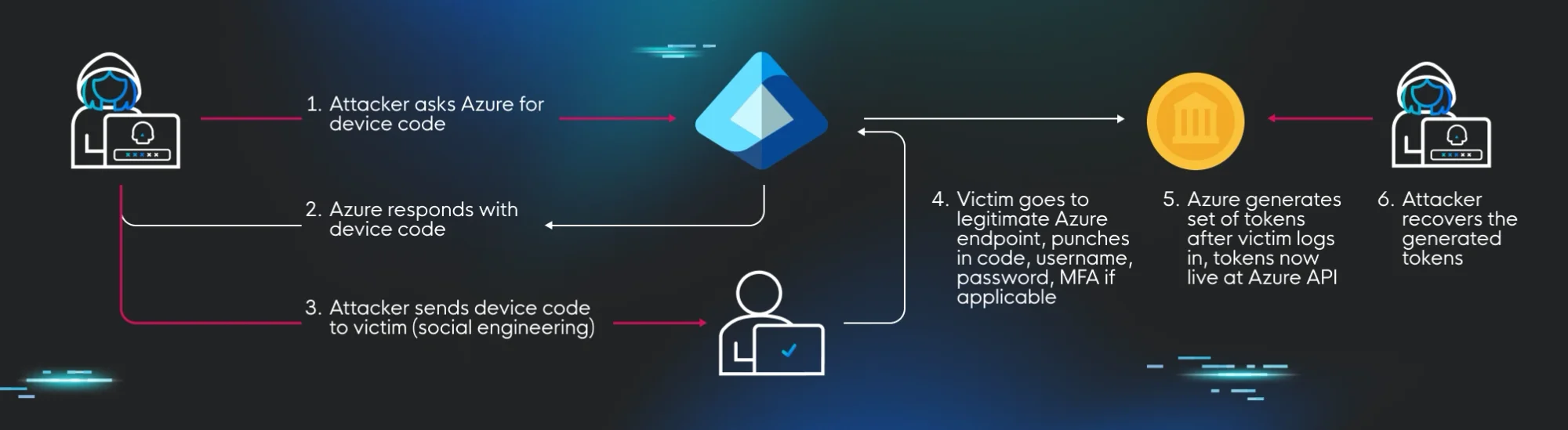
Unlike traditional phishing, which tries to steal your password, device code phishing abuses a completely legitimate Microsoft login process.
Here’s what happens behind the scenes, in simple terms:
- The attacker requests a device code from Microsoft’s system.
- You receive an email telling you to go to the real Microsoft device login page.
- You enter the code and sign in sometimes even completing MFA (multi‑factor authentication).
- Microsoft issues tokens that allow ongoing access.
- The attacker quietly collects those tokens and gains long‑term entry into your account.
And here’s the alarming part:
These tokens remain valid even after you change your password.
This means the attacker can stay logged in sometimes for weeks without you even noticing.
To make things even more convincing, the attackers now automatically generate and display these device codes on their phishing pages, removing the need for manual steps and making the process feel faster and more user‑friendly than the real one.
Behind the Scenes: What Makes This Scam Hard to Detect
Security researchers discovered several sneaky tricks built into the phishing pages to stop people and security tools from analyzing them. These include:
- Blocking right‑click
- Preventing text copying
- Detecting when developer tools are opened
- Triggering endless debugging loops
- Immediately stealing browser cookies when the page loads
All of these are designed to slow down investigators and make the attack harder to spot.
Who’s Behind It?
While the investigation is still ongoing, this campaign has strong similarities to previous activity linked to major threat groups like APT29, Storm‑2372, and other Russia‑aligned actors.
Huntress researchers say the attacks appear to be powered by a new phishing‑as‑a‑service platform called EvilTokens, which emerged on Telegram in early 2026. The service offers everything from automated phishing email campaigns and spam‑evasion tools to open redirect links and a dashboard for attackers to monitor their victims complete with customer support.
Cybercrime, it seems, is becoming increasingly polished and professional.
Final Thoughts
This rapidly expanding phishing campaign shows just how creative cybercriminals have become. By blending trusted cloud platforms, clever social engineering, and legitimate Microsoft login flows, attackers are able to trick even security-conscious users.
Understanding how device code phishing works and recognizing the signs is one of the best ways to stay ahead of these threats. Cybersecurity may seem complex, but awareness is one of the most powerful tools we have.
Stay protected with TechSquad!
Reliable technology is the backbone of every successful business. With TechSquad’s IT services in Valdosta, you get more than support you get a partner who’s invested in your success. From cybersecurity to cloud solutions, we deliver the tools, expertise, and responsiveness your business needs to thrive.

